Why the CRA — and Why Now
The Cyber Resilience Act is among the most consequential cybersecurity regulations introduced by the
European Union for digital products. Adopted by the European Parliament and Council on 23 October 2024
and published in the Official Journal three weeks later, the regulation is now binding law across all
27 Member States. Unlike a directive, it requires no national transposition — implementation timelines
are already in effect.
Three dates matter. The CRA entered into force on 10 December 2024. From
11 September 2026, manufacturers must submit a CRA early-warning notification within
24 hours of becoming aware of an actively exploited vulnerability — a hard, non-negotiable deadline
that applies to legacy products as much as to new ones. Then on 11 December 2027, the
full body of obligations takes effect: secure-by-design engineering, conformity assessment, CE marking,
lifecycle support, and Software Bill of Materials transparency.
10 Dec 2024
CRA Enters Into Force
Directly applicable in all 27 EU Member States. No transposition required.
11 Sep 2026
Reporting Obligations Begin
24-hour mandatory reporting for actively exploited vulnerabilities — including legacy products.
11 Dec 2027
Full Compliance Mandatory
CE marking, secure-by-design, SBOM, conformity assessment and lifecycle support all required.
The Cybersecurity Landscape — By the Numbers
The CRA did not arrive in a vacuum. It is the European Union's structured response to a measurable,
sustained deterioration in the security posture of digital products entering its market.
USD 4.44M
Global average cost of a data breach (IBM & Ponemon, 2025).
+34%
Year-on-year increase in vulnerability exploitation as a breach vector (Verizon DBIR 2025).
21.1B
Connected IoT devices forecast worldwide by end of 2025 (IoT Analytics).
€15M
Maximum CRA penalty — or 2.5% of global turnover (Article 64(2)).
The CRA is not reacting to a future problem — it is responding to an already measurable
failure in digital product security.
What the CRA Actually Requires
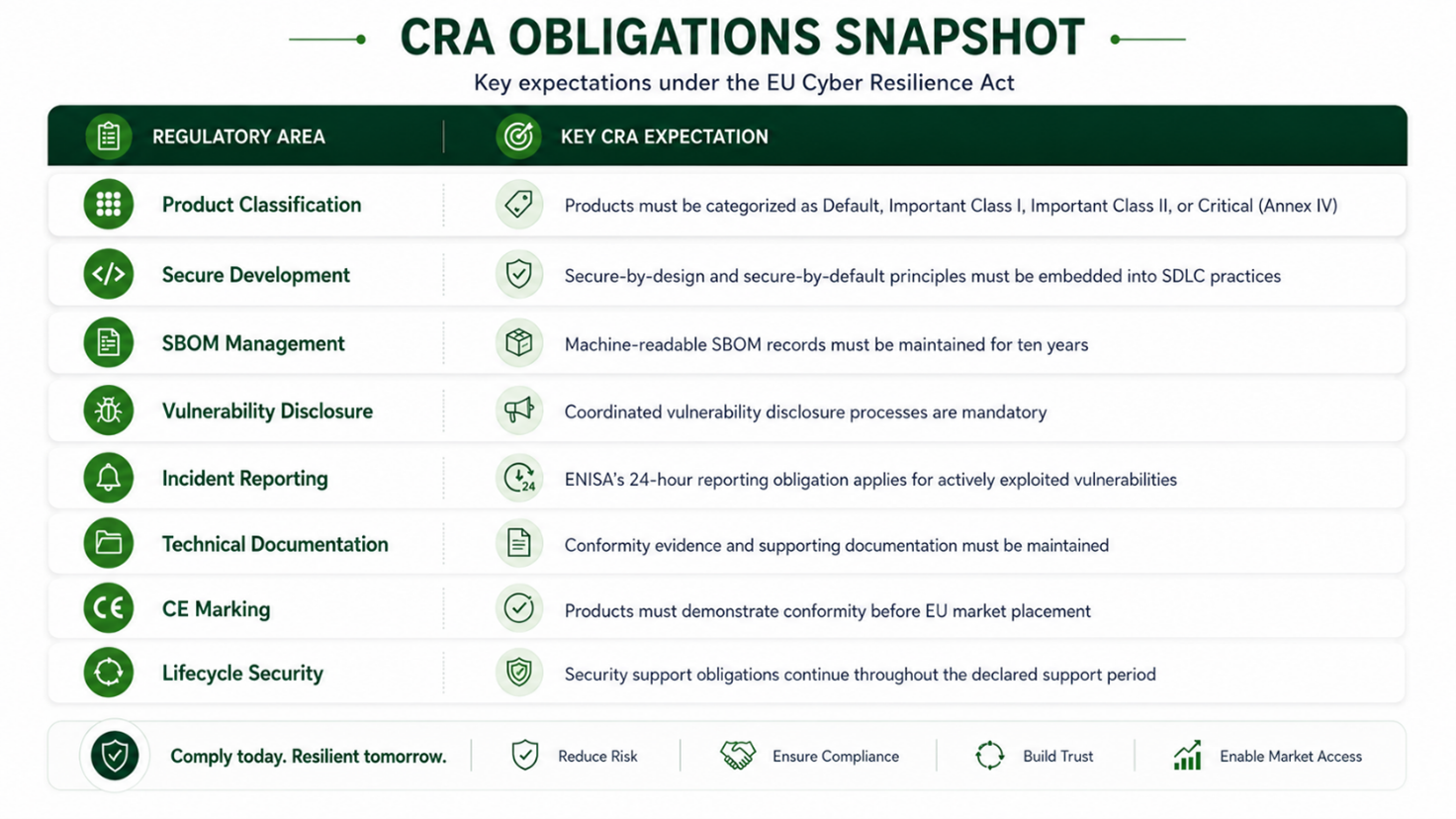
The regulation imposes structured obligations across the product lifecycle. Manufacturers must classify
their products into one of four risk tiers —
Default, Important Class I, Important Class II, or Critical — each with distinct
conformity assessment routes (Articles 7, 8 and 32 of Regulation (EU) 2024/2847; Annexes III and IV;
technical descriptions in Commission Implementing Regulation (EU) 2025/2392).
The FORTEIA CRORF Framework
FORTEIA's CRA Readiness & Operational Resilience Framework (CRORF) provides a
structured, phased path to compliance. Cross-functional alignment — security, engineering, legal,
and product — is essential throughout.
